Kaspersky researchers identified a powerful malware Android application, lurking in adult content and fake virus scanners, that secretly mines cryptocurrency on affected smartphones, and can physically damage the device if it is not detected.
Nikita Buchka, Anton Kivva, Dmitry Galov of cybersecurity firm Kaspersky investigated the malware, calling it A Jack Of All Trades, because of its modular architecture that allows it to be adapted to perform cryptocurrency mining, take part in or launch DDoS attacks, bombard the smartphone owners with constant ads and much more.
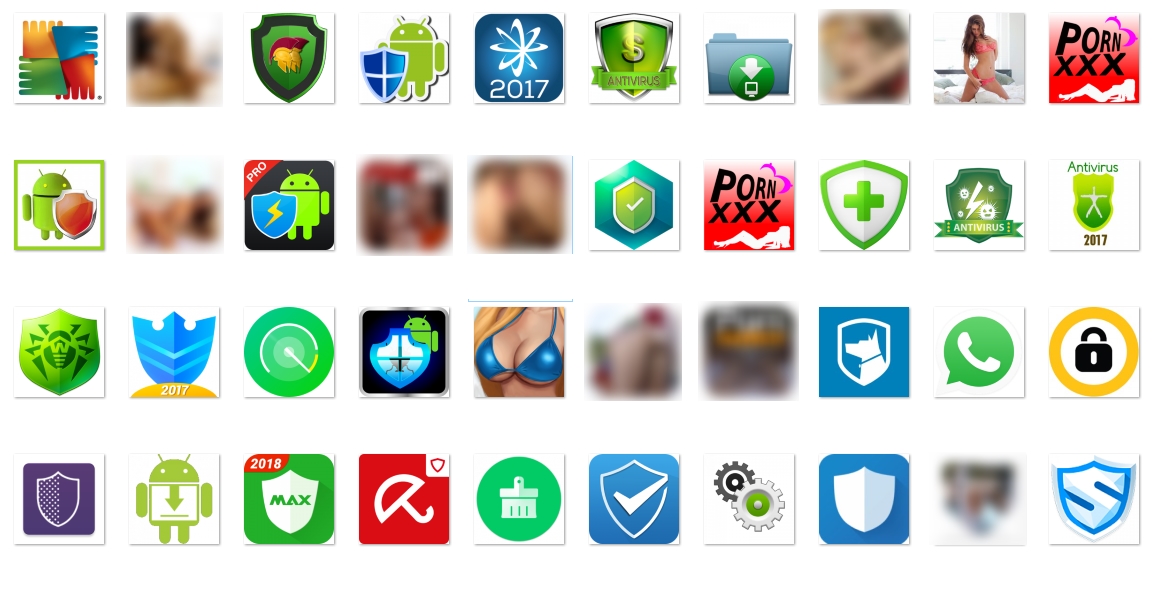
The new malware is officially named Trojan.AndroidOS.Loapi and it has been found hiding in Android applications downloaded by infected sites, not Google Play Store. These apps are distributed via advertising campaigns. The user is redirected to the attackers’ website, and then the malicious files are downloaded. At the moment, there have been found more than 20 such websites, whose domains refer to popular antivirus solutions and even a famous porn site. The image below shows a variety of antivirus solutions or adult content apps where Loapi mainly hides behind:
One of Loapi's abilities is that it can hijack the CPU of the smartphone and use it to mine the Monero cryptocurrency. What is scarier is that the Loapi malware physically broke a test phone, after the researchers let it run for two days. "Because of the constant load caused by the mining module and generated traffic, the battery bulged and deformed the phone cover," the Kaspersky blog states.
The malware application tries to obtain device administrator permissions, asking for them in a loop until the user agrees. If the user tries to take away these permissions, Loapi locks the screen and closes the window with device manager settings!
After it gets admin privileges, the Loapi malware either hides its icon in the menu or simulates various antivirus application activity, depending on the type of application it masquerades as:
The malware consists of 5 modules:
- Advertisement module, used for the aggressive display of advertisements on the user’s device
- SMS module, used for different manipulations with text messages. It also periodically sends requests to the C&C server to obtain relevant settings and commands.
- Web crawling module, used for hidden Javascript code execution on web pages with WAP billing in order to subscribe the user to various services.
- Proxy module, an implementation of an HTTP proxy server that allows the attackers to organize DDoS attacks against specified resources.
- Mining module, which uses the Android version of minerd to perform Monero (XMR) cryptocurrency mining.
