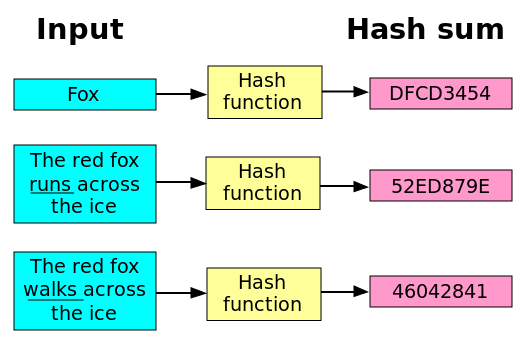
A Hash Function is a mathematical algorithm which, given an input (called message: number, text or both) of any length, it produces an almost-unique output (called "hash value", "hash sum", "digest" or plain "hash") of a fixed length.
In other words, a Hash Function maps data of arbitrary size to data of fixed size.
Hash functions are used in computer software for rapid data lookup. They are also very useful in cryptography.
Cryptographic hash functions are a special class of hash functions which have the property that given a hash value, it is extremely difficult to compute for which input (or message) the function produced that specific hash.
At the same time, given a pair of input and output (message and sum), hash functions allow us to quickly verify if the specific input leads to the given output.
Cryptographic hash functions have these five main properties:
- They are deterministic: the same message always results in the same hash
- They are quick to compute the hash value for any given message
- It is infeasible to generate a message from its hash value except by trying all possible messages
- A small change to a message should change the hash value so extensively that the new hash value appears uncorrelated with the old hash value
- It is infeasible to find two different messages with the same hash value (Collision resistance)
Cryptographic Hash Functions are used in Bitcoin mining and other cryptocurrencies in general. The Proof-of-Work system used in Bitcoin and Hashcash uses partial hash inversions to prove that some work was done. In Bitcoin these inversions unlock a "reward" (new bitcoins attributed to miners) whereas in Hashcash, they are used as a good-will token to send an e-mail.